This blog will provide the highlevel steps to install an ifixes on IBM Connections 4.5 CR 5.
Note: These steps are generic in nature and would apply for most of the ifix in connections unless specified by the PMR team or documented in the ReadMe of that ifix
Env: IBM Connections 4.5 CR 5
iFixes to be installed :
4.5.0.0-IC-News-IFLO75278.jar
4.5.0.0-IC-News-IFLO75278-OSGi.jar
IBM connections Installation Path : /opt/IBM/Connections
Step1: Ensure that the ifixes are not already installed
a. Run the setupCmdLine.sh to load the env setting for the Connections
| [root@connections1 /]$ . /opt/IBM/WebSphere/AppServer/profiles/Dmgr01/bin/setupCmdLine.sh |
NOTE: the updateSilent.sh command will not launch if the setupCmlLine.sh is not executed
b. Navigate to where the updateInstaller is located , in my case its /opt/IBM/Connections/updateInstaller
| [[root@connections1 /]$cd /opt/IBM/Connections/updateInstaller |
c. Run the updateSilent.sh with the attributes mentioned below
| [root@connections1 updateInstaller]$ ./updateSilent.sh -fix -installDir /opt/IBM/Connections | grep 75278 |
Where 75278 is the ifix Number which we are going to install
We don’t have the ifixes installed so proceed with the downloading of the ifixes
Step2: Download the Fixpack from the Fixcentral based on your environment and your issues
We will downloading the ifix 4.5.0.0-IC-News-IFLO75278.jar & 4.5.0.0-IC-News-IFLO75278-OSGi.jar
NOTE :For the ifix to be installed the Fix Central will recommend the prerequisite updateInstaller
which needed to be installed
Download the following
4.5.0.0-IC-News-IFLO75278.jar
4.5.0.0-IC-News-IFLO75278-OSGi.jar
And also download the UPDI which is required to install the above ifix
4.5.0.0-IC-Multi-UPDI-20131020.zip
=================================================================
NOTE : This is needed only if your updateInstaller is not of the same version
To check the version of the updateInsaller
a. Navigate to /opt/IBM/Connections/updateInstaller/version
| bash-3.2$ [root@connections1 /]$ cd /opt/IBM/Connections/updateInstaller/version |
b. Open lcui.product file
| [root@connections1 version]$ more lcui.product‘<!DOCTYPE product SYSTEM “product.dtd”> ‘<product name=”Update Installer for IBM Connections”> ‘<id>lcui</id> ‘<version>4.5.0.0</version> ‘<build-info date=”10/20/2013” level=”00000001″/> ‘</product> [root@connections1 version]$ |
Which is 4.5.0.0-IC-Multi-UPDI-20131020.zip
If the version are same as the one required by the ifix you don’t need to upgrade your updateInstaller
===================================================================
Step3: Installation of the New updateInstaller 4.5.0.0-IC-Multi-UPDI-20131020.zip
NOTE: This step is needed only if the updateInstaller is lower that the one required by the ifixes
a. Extract the 4.5.0.0-IC-Multi-UPDI-20131020.zip
b.Take the backup of the existing updateInstaller in the location /opt/IBM/Connections/
| [root@connections1 Connections]$cd /opt/IBM/Connections/ [root@connections1 Connections]$mv updateInstaller updateInstaller.backup |
c. Extract the file 4.5.0.0-IC-Multi-UPDI-20131020.zip in the location /opt/IBM/Connections
And make the scripts executable with chmod 755 *.sh if it is not in executable
| [root@connections1 updateInstaller]$chmod –R 755 *.sh |
That’s It .. This will install the updateInstaller
Step4: Take the necessary backup
a. Take the backup of the Connections Customization Directory. You could take a tarzip
backup or copy it in a backup location
NOTE : To get the Customization Directory
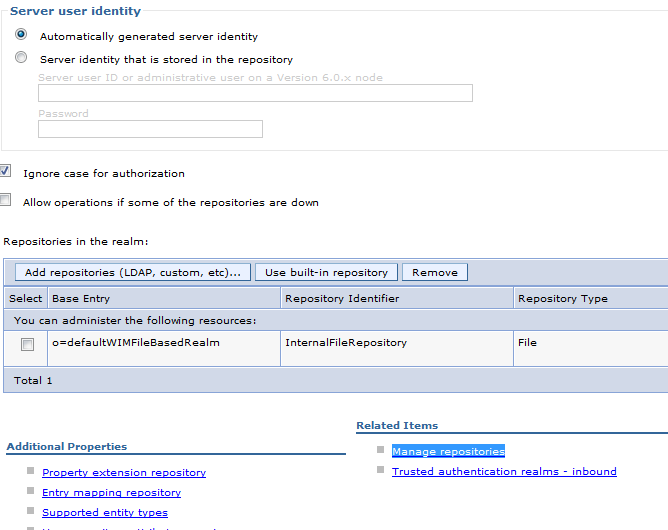
Login to the connections admin console >>
WebSphere Variables >>CONNECTIONS_CUSTOMIZATION_PATH
| [root@connections1 ifixes]$ cp -r /share/customization/ /backup/customization.backup |
b. Take the backup of the LotusConnections-config from the Dmgr Cell
| [root@connections1 updateInstaller]$ cd /opt/IBM/WebSphere/AppServer/profiles/Dmgr01/config/cells/connectionsCell01/ [root@connections1 connectionsCell01]$ cp -r LotusConnections-config/ /backup/LotusConnections-config.backup |
c. Take the copy of the Existing ifixes installed for references
For Eg.
| [root@connections1 updateInstaller]$ . /opt/IBM/WebSphere/AppServer/profiles/Dmgr01/bin/setupCmdLine.sh [root@connections1 updateInstaller]$ ./updateSilent.sh -fix -installDir /opt/IBM/Connections > /backup/VersionDetails_BeforeIfix.txt |
d. Take the Backup of the specific Database if the ifix modifies some changes in the DB
Step5: Installation of the Ifix
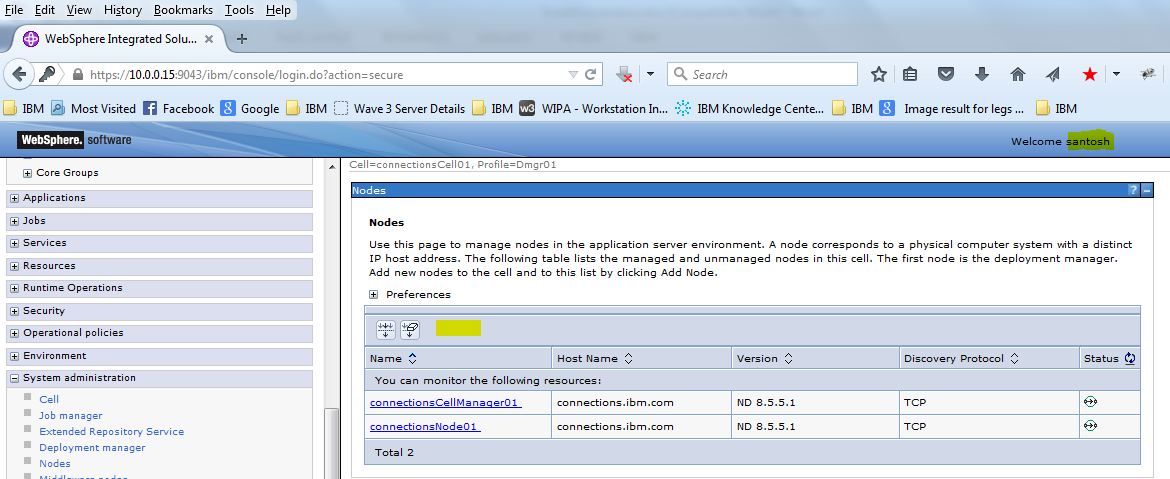
1. Stop the Connections Servers Servers and the Nodeagent
2. Ensure the dmgr is started Otherwise during the UpdateWizard will not be able to proceed further
3. Copy the ifix which were downloaded from the fixcentral to the ifixes folder in updateInstaller Folder , Though It can be any location within the server
| [root@connections1 updateInstaller]$ mkdir /opt/IBM/Connections/updateInstaller/ifixes |
The Files were transferred using Winscp
| [root@connections1 updateInstaller]$ ls -l ifixes |
4. Launch the GUI Console of RHEL Server
As root ( or any user with which the installation was done) launch the GUI Console of the
RHELServer using VNC or Xming or any X11 forwarding tools
5. Run setupCmdLine.sh to load the env variables
| [root@connections1 updateInstaller]$ . /opt/IBM/WebSphere/AppServer/profiles/Dmgr01/bin/setupCmdLine.sh |
NOTE: the updateWizard.sh command will not launch if the setupCmdLine.sh is not executed
6. Then Launch the updateWizard.sh from the GUI from the path /opt/IBM/Connections/updateInstaller
7. Click Next on the welcome screen
8. Select the “Install updates ” Option and provide the Path of the ifixes folder .
In my case its /opt/IBM/Connections/updateInstaller/ifixes.
Then click Next
9. The updateWizard will detect the ifixes in that folder . We had copied two ifixes
4.5.0.0-IC-News-IFLO75278.jar
4.5.0.0-IC-News-IFLO75278-OSGi.jar
We can click “Details” if we want more information on these ifixes
Select both the ifixes and click Next
NOTE: If there are any dependencies ifixes requirement it will be prompted
10. The updateWizard will provide a message to take the necessary backups before the installation.
Check the box and Click OK
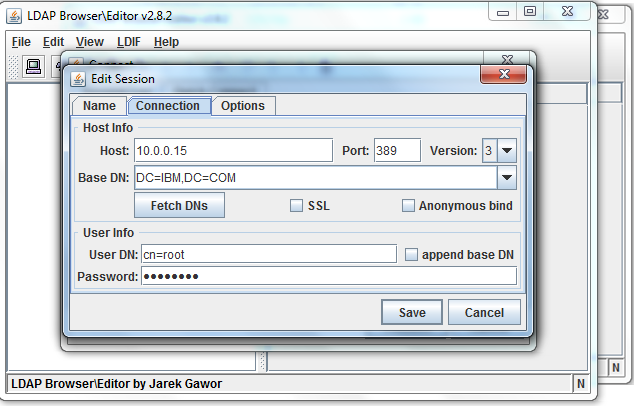
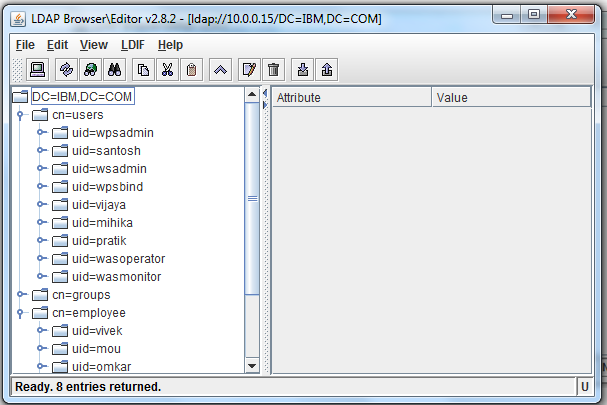
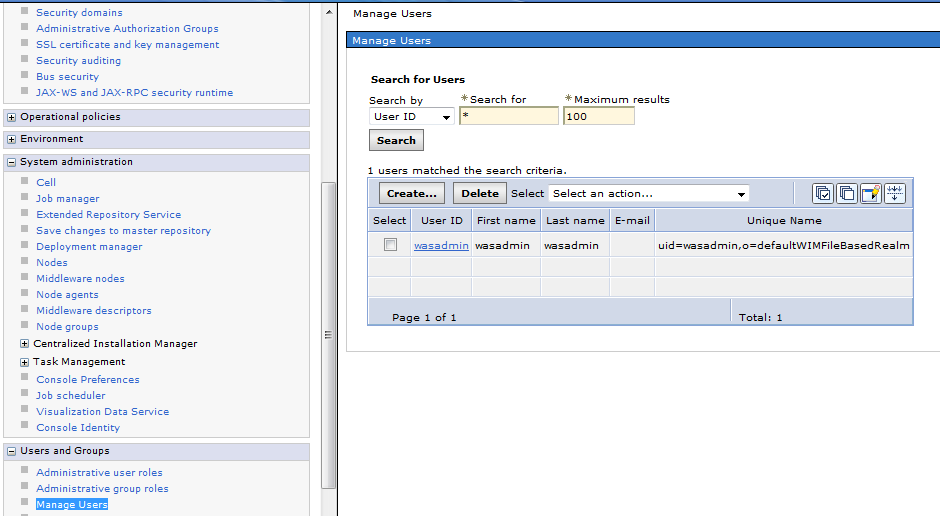
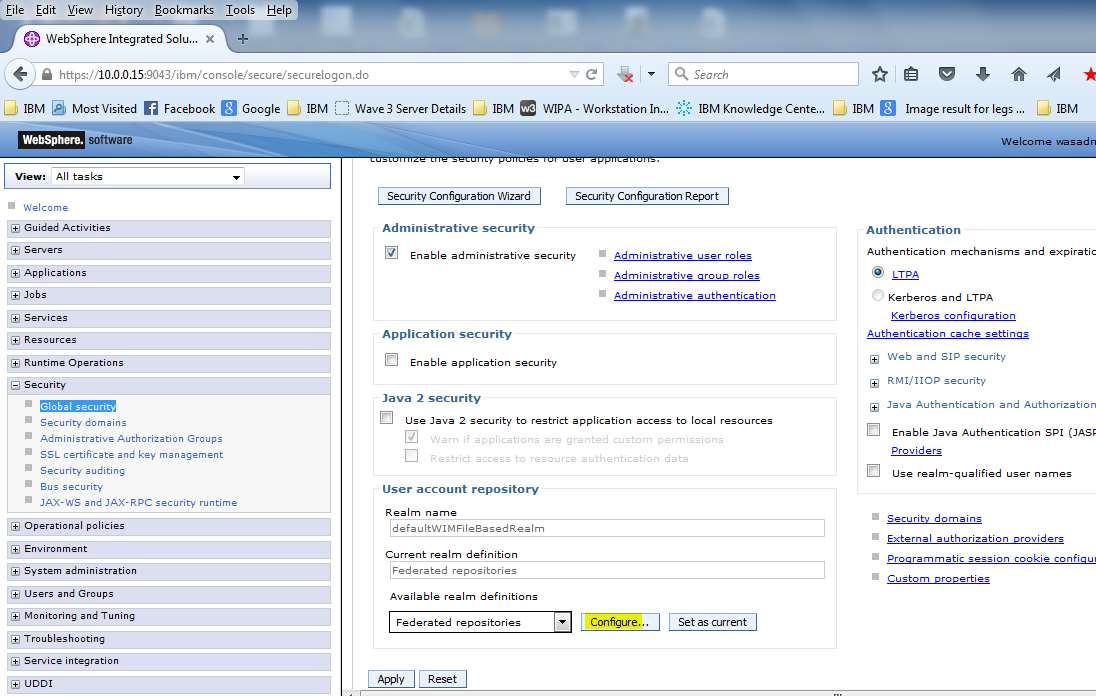
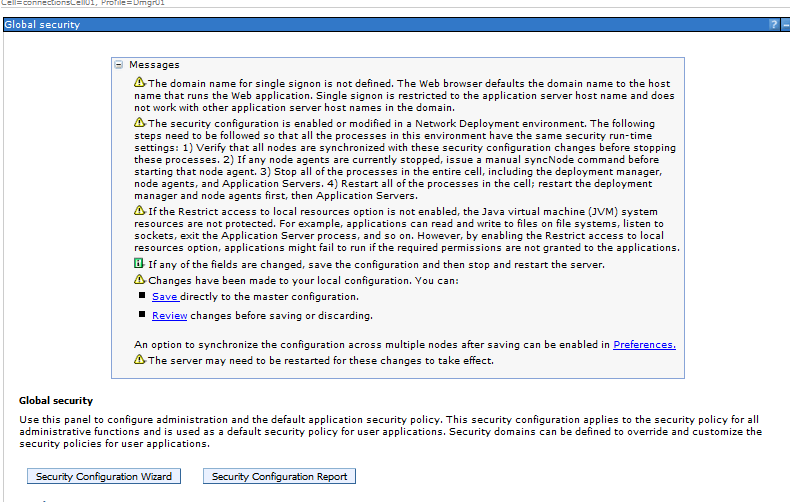
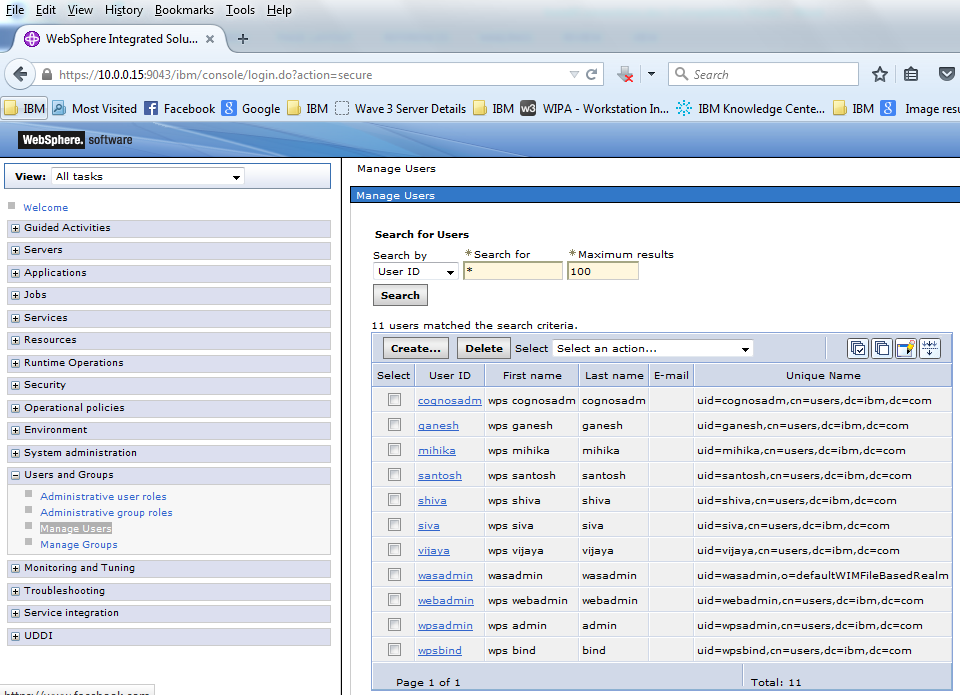
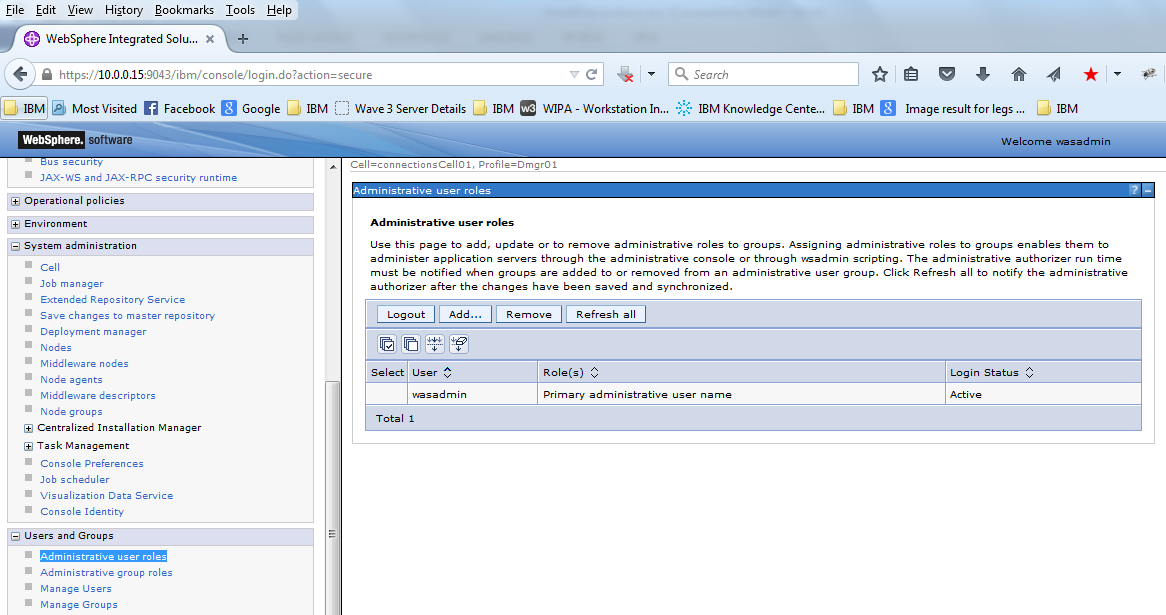
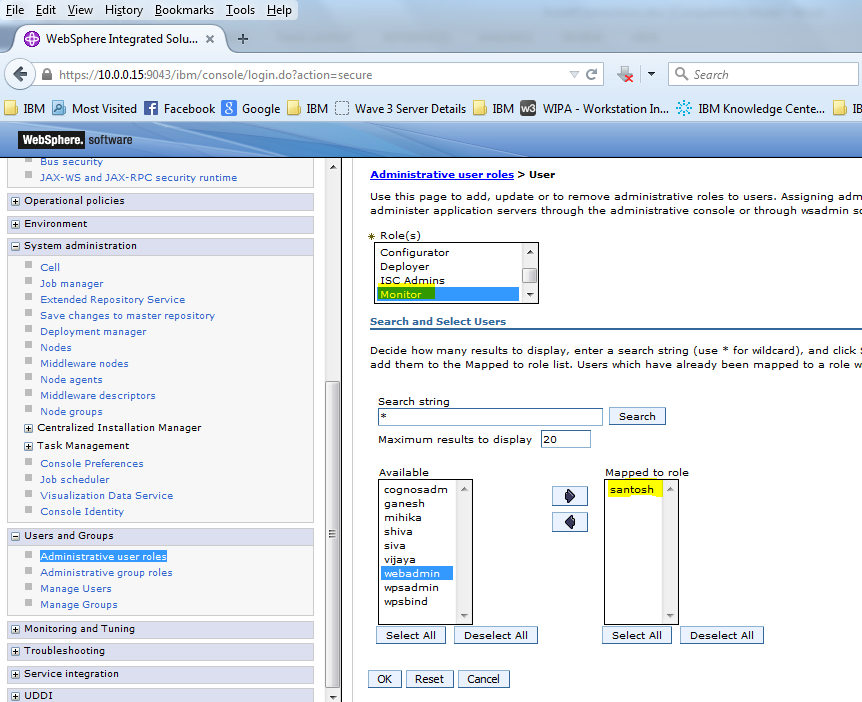
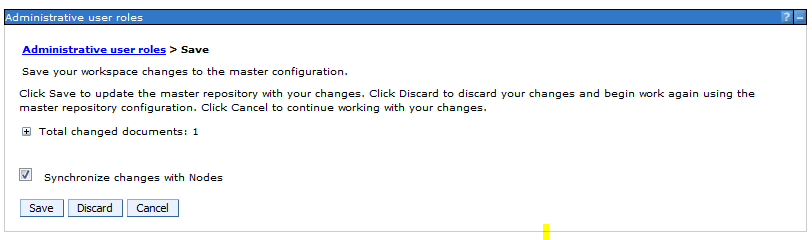
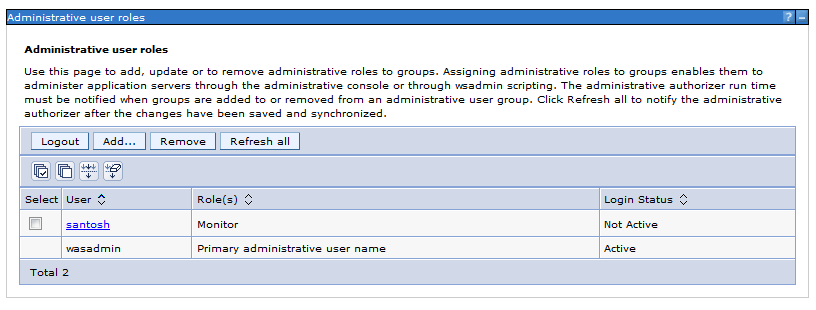
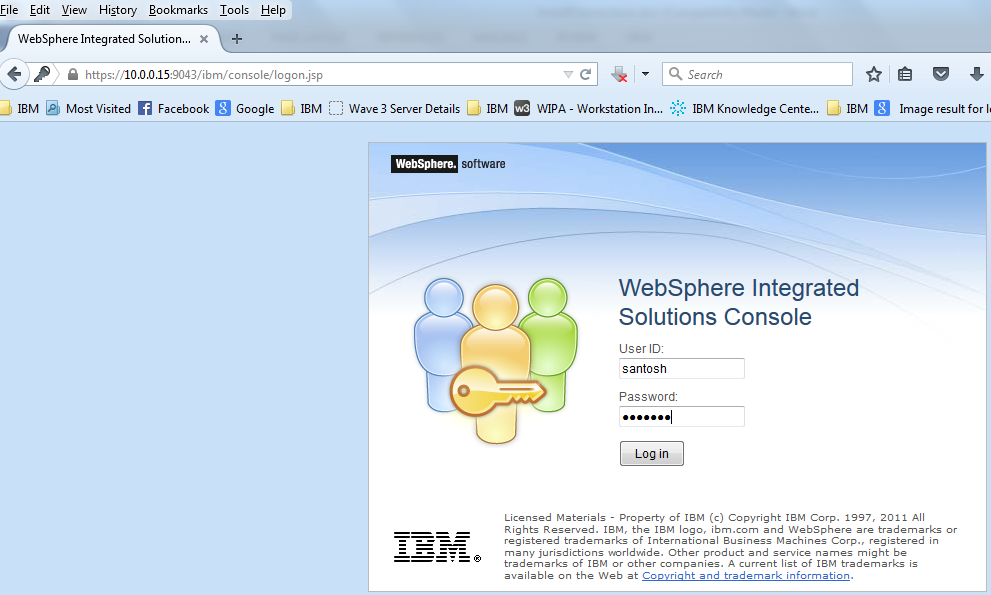
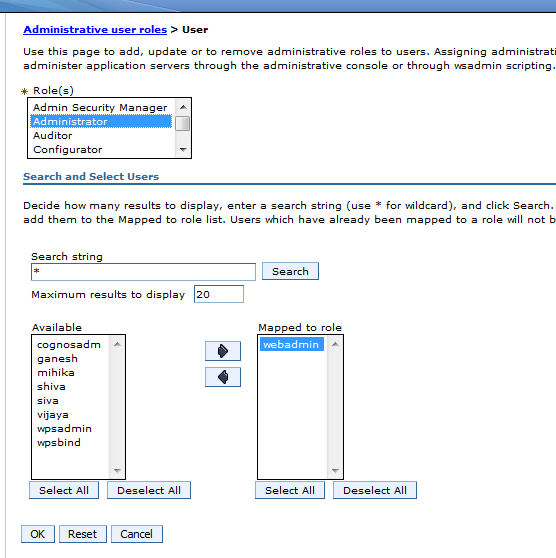
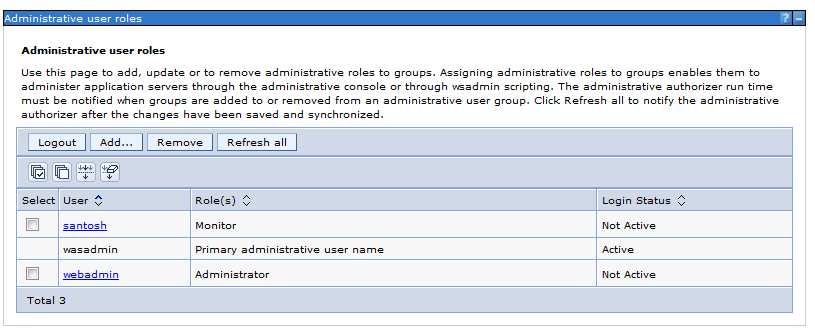
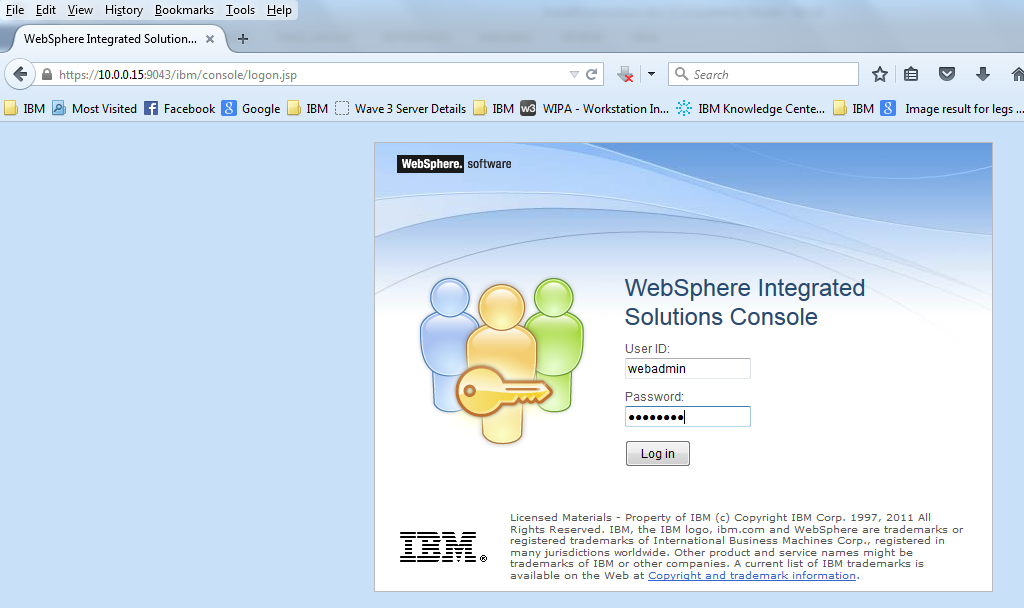
11. Provide the Deployment Manager Admin user name and Password . This will be validated to proceed
l2. After the Validation Successful .. Click OK
13. Check the summary page . it will again display the ifixes which we have selected to Install
Click Install
Note : It may take some time depending on the number of ifixes
14. The logs are created in the /opt/IBM/Connections/version/log/
Tail the logs for the ifixes
| [root@connections1 log]$ cd /opt/IBM/Connections/version/log/ [root@connections1 log]$tail –f 20151107_032631_LO75278-OSGi_news_install.log |
15. If the iFIx installation was successful we will get a “ Result: The iFix Installation was successful”
message in the updateWizard
Checks the logs too . The BUILD SUCESSFUL message should be displayed in them
===============================================================================
NOTE: The Installation of the ifix can be done using command line too
For example:
| [root@connections1 updateInstaller]$./updateSilent.sh -installDir /opt/IBM/Connections -fix -fixDir /opt/IBM/Connections/update/ifixes -install -fixes LO75278 LO75278-OSGi -wasUserId wasadmin -wasPassword <password> -featureCustomizationBackedUp yes |
=============================================================================
16. Validate if the ifix is installed
| [root@connections1 log]$ cd /opt/IBM/Connections/updateInstaller |
a. Run setupCmdLine.sh
| [root@connections1 /]$ . /opt/IBM/WebSphere/AppServer/profiles/Dmgr01/bin/setupCmdLine.sh |
b. Run updateScript.sh with the options mentioned below
| [root@connections1 updateInstaller]$ ./updateSilent.sh -fix -installDir /opt/IBM/Connections | grep 75278 |
We see that the ifixes for LO75278 is installed
17. Restart Dmgr and Check the dmgr logs
Stop Dmgr
| [root@connections1 /]$ cd /opt/IBM/WebSphere/AppServer/profiles/Dmgr01/bin/stopManager.sh |
Provide the wasadmin credentials while stopping
Start dmgr
| [root@connections1 /]$ cd /opt/IBM/WebSphere/AppServer/profiles/Dmgr01/bin/startManager.sh |
18. Start the nodeagent , Do a full synchronization
| [root@connections1 /]$ /opt/IBM/WebSphere/AppServer/profiles/AppSrv01/bin/startNode.sh |
- Start the Sever , and check the logs for any errors
In this way we can install the Ifixes for on IBM connections 4.5